24/7 Managed Detection and Response Services
INTRODUCTION
CyberNX - Your Trusted MDR Partner

We address your key challenges:
How It Works?
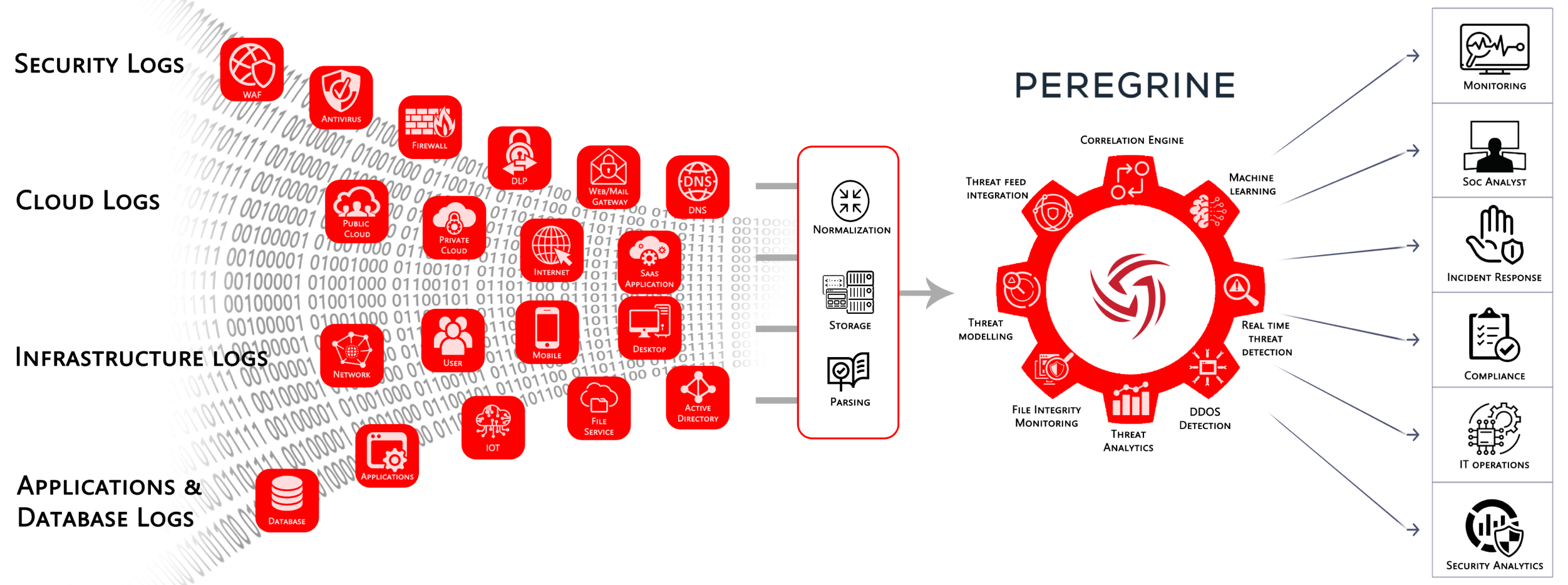
APPROACH
Why Choose CyberNX as Your MDR Partner?
01
Threat modeling
02
Log Assessment
03
Use Case Customization
04
Dedicated Threat Hunting
05
Customized Reporting
06
Functional SME Team
Looking for MDR Services?
Connect with Our Cybersecurity Experts!

BENEFITS
Maximizing Threat Visibility with MDR Services
Expertise That Matters
Our cybersecurity team comprises seasoned professionals adept in threat detection, incident response, and vulnerability management.
Cutting-edge Technology
We utilize advanced tools, global threat intelligence, machine learning, and generative AI to provide unparalleled visibility into potential threats.
Rapid Incident Response
Swift action minimizes impact and downtime, swiftly addressing security incidents to ensure operational continuity.
Cost-Effectiveness
Outsourcing security services can be more economical than maintaining an in-house team, optimizing resource allocation.
Enhanced Visibility
Gain comprehensive insights into your security posture, vulnerabilities, and risks to facilitate informed decision-making for stronger defenses.
Peace of Mind
With your organization's security in capable hands, you can focus on core business activities with confidence.
TESTIMONIALS
Hear from Our Satisfied Clients about CyberNX
“Best partners you can find for your Cloud Security journey.”
As a CISO what you look for a partner is passion, zeal and ownership for the project. I found all this in our work with Cyber NX, a niche firm specialising in Cloud Security. When I was looking for someone to audit our Cloud environment and make a roadmap for enhancing security I found a lot of vendor who shared high level frameworks. However, it was CyberNX who gave a specific and detailed gap assessment methodology. Their final report and roadmap helped us improve our Cloud Security posture and mitigate critical risks. CyberNX and their founder Bhowmik Shah are the best partners you can find for your Cloud Security journey.

“Best partners you can find for your Cloud Security journey.”
As a CISO what you look for a partner is passion, zeal and ownership for the project. I found all this in our work with Cyber NX, a niche firm specialising in Cloud Security. When I was looking for someone to audit our Cloud environment and make a roadmap for enhancing security I found a lot of vendor who shared high level frameworks. However, it was CyberNX who gave a specific and detailed gap assessment methodology. Their final report and roadmap helped us improve our Cloud Security posture and mitigate critical risks. CyberNX and their founder Bhowmik Shah are the best partners you can find for your Cloud Security journey.

“Best partners you can find for your Cloud Security journey.”
As a CISO what you look for a partner is passion, zeal and ownership for the project. I found all this in our work with Cyber NX, a niche firm specialising in Cloud Security. When I was looking for someone to audit our Cloud environment and make a roadmap for enhancing security I found a lot of vendor who shared high level frameworks. However, it was CyberNX who gave a specific and detailed gap assessment methodology. Their final report and roadmap helped us improve our Cloud Security posture and mitigate critical risks. CyberNX and their founder Bhowmik Shah are the best partners you can find for your Cloud Security journey.

PLANS
Choose A Plan For MDR Services
Plans for all business |
Bronze For starter companiesSelect Plan |
Silver For small companiesSelect Plan |
Gold For mid-size companiesSelect Plan |
Platinium For large companiesSelect Plan |
24 X 7 Security Monitoring |
 |
 |
 |
 |
Log collection and Aggregation |

|

|

|

|
Log retention |
15 Days |
20 Days |
30 Days |
30 Days |
Correlation of Logs |

|

|

|

|
Machine Learning Detections |

|

|

|

|
Custom Dashboards |

|

|

|

|
Cloud Security Posture Monitoring (CSPM) |

|

|

|

|
Cloud Vulnerability Management (CNVM) |

|

|

|

|
Weekly Threat Hunting Reports |

|

|

|

|
Commercial Threat Intelligence |

|

|

|

|
Brand Reputation Monitoring (BRM) |

|

|

|

|
Automated Reports |
Monthly |
Monthly |
Daily and Weekly |
Daily and Weekly |
Governance Calls |

|
Qaurterly |
Monthly |
Weekly |
Long term log retention |
Optional |
Optional |
Optional |
Optional |
For Customized Plans tailored to Your Needs,
Get in Touch Today!
RESOURCES
Cyber Security Knowledge Hub
BLOGS
CASE STUDIES
DOWNLOADS
FAQ
Frequently Asked Questions
- 24/7 Monitoring and Detection: Continuous surveillance of your IT environment to identify and respond to threats in real time.
- Threat Hunting: Proactive search for threats that might evade automated detection systems.
- Incident Response: Rapid response to security incidents to mitigate impact and reduce recovery time.
- Advanced Analytics: Use of machine learning and AI to enhance threat detection and analysis.
- Compliance Support: Ensuring adherence to industry regulations and standards.